A suspected Vietnamese-origin threat actor has been observed targeting victims in several Asian and Southeast Asian countries with malware designed to harvest valuable data since at least May… Continue reading
Category: Hacker news
Apr 04, 2024NewsroomVulnerability / Internet Protocol New research has found that the CONTINUATION frame in the HTTP/2 protocol can be exploited to conduct denial-of-service (DoS) attacks. The technique… Continue reading
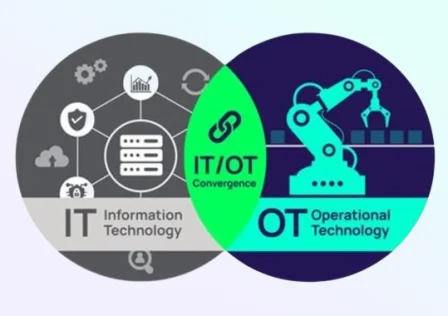
Operational Technology (OT) refers to the hardware and software used to change, monitor, or control the enterprise’s physical devices, processes, and events. Unlike traditional Information Technology (IT) systems,… Continue reading
Apr 04, 2024NewsroomNetwork Security / Vulnerability Ivanti has released security updates to address four security flaws impacting Connect Secure and Policy Secure Gateways that could result in code… Continue reading
Apr 03, 2024NewsroomBrowser Security / Session Hijacking Google on Tuesday said it’s piloting a new feature in Chrome called Device Bound Session Credentials (DBSC) to help protect users… Continue reading
Apr 03, 2024NewsroomMobile Security / Zero Day Google has disclosed that two Android security flaws impacting its Pixel smartphones have been exploited in the wild by forensic companies…. Continue reading
Apr 03, 2024NewsroomData Breach / Incident Response The U.S. Cyber Safety Review Board (CSRB) has criticized Microsoft for a series of security lapses that led to the breach… Continue reading
Apr 03, 2024The Hacker NewsCybersecurity / Penetration Testing Attack surface management (ASM) and vulnerability management (VM) are often confused, and while they overlap, they’re not the same. The… Continue reading
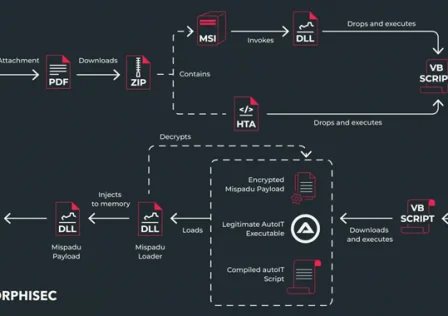
The banking trojan known as Mispadu has expanded its focus beyond Latin America (LATAM) and Spanish-speaking individuals to target users in Italy, Poland, and Sweden. Targets of the… Continue reading
Apr 03, 2024NewsroomWeb Security / Vulnerability A critical security flaw impacting the LayerSlider plugin for WordPress could be abused to extract sensitive information from databases, such as password… Continue reading