Apr 26, 2024NewsroomMobile Security / Cybercrime Fake browser updates are being used to push a previously undocumented Android malware called Brokewell. “Brokewell is a typical modern banking malware… Continue reading
Tag: Malware
Apr 24, 2024NewsroomMalware / Data Security A new ongoing malware campaign has been observed distributing three different stealers, such as CryptBot, LummaC2, and Rhadamanthys hosted on Content Delivery… Continue reading
Apr 23, 2024NewsroomNational Security Agency / Threat Intelligence The Russia-linked nation-state threat actor tracked as APT28 weaponized a security flaw in the Microsoft Windows Print Spooler component to… Continue reading
Apr 18, 2024NewsroomIncident Response / Cyber Espionage Select Ukrainian government networks have remained infected with a malware called OfflRouter since 2015. Cisco Talos said its findings are based… Continue reading
Sandboxes are synonymous with dynamic malware analysis. They help to execute malicious files in a safe virtual environment and observe their behavior. However, they also offer plenty of… Continue reading
Apr 16, 2024NewsroomThreat Intelligence / Endpoint Security The threat actor tracked as TA558 has been observed leveraging steganography as an obfuscation technique to deliver a wide range of… Continue reading
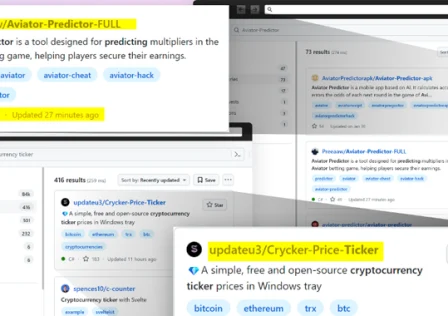
Apr 10, 2024NewsroomSoftware Security / Supply Chain Attack Threat actors are now taking advantage of GitHub’s search functionality to trick unsuspecting users looking for popular repositories into downloading… Continue reading
Apr 10, 2024NewsroomCyber Crime / Malvertising Cybersecurity researchers have discovered a new Raspberry Robin campaign wave that propagates the malware through malicious Windows Script Files (WSFs) since March… Continue reading
Apr 09, 2024NewsroomMalware / Cryptojacking Cybersecurity researchers have discovered an intricate multi-stage attack that leverages invoice-themed phishing decoys to deliver a wide range of malware such as Venom… Continue reading
Apr 09, 2024NewsroomBotnet / Vulnerability Threat actors are actively scanning and exploiting a pair of security flaws that are said to affect as many as 92,000 internet-exposed D-Link… Continue reading